Creating a simple network map helps you quickly find unknown devices by providing an overview of connected devices. Start by using a network scanner that offers real-time updates and device identification. Visualize your network layout and cross-check IP and MAC addresses to spot unfamiliar devices. Ensuring your scanner has proper permissions and understands network segments can improve detection. Keep it clear and expand your map gradually — if you follow these steps, you’ll uncover more about your network’s hidden devices.
Key Takeaways
- Use a network scanner with real-time updates to detect and identify all connected devices instantly.
- Cross-reference device IPs, MAC addresses, and manufacturer details to spot unfamiliar devices.
- Visualize your network topology to easily spot devices outside expected connections.
- Regularly update and expand your network map for comprehensive device visibility.
- Check device behavior and communication patterns to identify potential unknown or rogue devices.

Xiiaozet Wireless USB Server and Print Server Share USB Devices (Printer, Scanner or More) Over LAN via Ethernet or WiFi Network Easy Setup Compatible with Windows Mac and Linux Virtual USB (LK300EW)
Multi-Function Device: Serves as both a USB server and print server, enabling multiple computers on the same network…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Why Creating a Network Map Helps You Find Unknown Devices

Have you ever wondered how to quickly identify unknown devices on your network? Creating a network map makes this process easier by giving you a clear overview of all connected devices. With a detailed map, you can spot unfamiliar devices instantly, improving device identification. This visual tool helps you recognize authorized gadgets and flag suspicious ones, bolstering your network security. When you understand what’s connected, you can monitor activity more effectively and respond to potential threats faster. A network map acts as your first line of defense, reducing the risk of unauthorized access. By regularly updating it, you stay ahead of new devices joining your network. Additionally, understanding your network’s device identification capabilities can help you better distinguish between legitimate and unknown devices. Incorporating natural pools and other backyard features into your planning can inspire innovative ways to visualize and understand your network environment, especially in complex setups. Recognizing the importance of network topology can further optimize your ability to manage and secure your network. Ultimately, a thorough network map simplifies managing your network’s security and keeps your connected environment safe.

VETOUCH Plug-in Carbon Monoxide Detector with Digital Color Display CO Detector for CO, Temperature & Humidity, 85dB Loud Alert, Self Test Function vetouch CO Detector, for Home, Bedroom, Kitchen, RV
【Plug-in CO Detector】Plug-and-use real-time vetouch CO detector with built-in temperature and humidity sensors for comprehensive air quality monitoring.
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
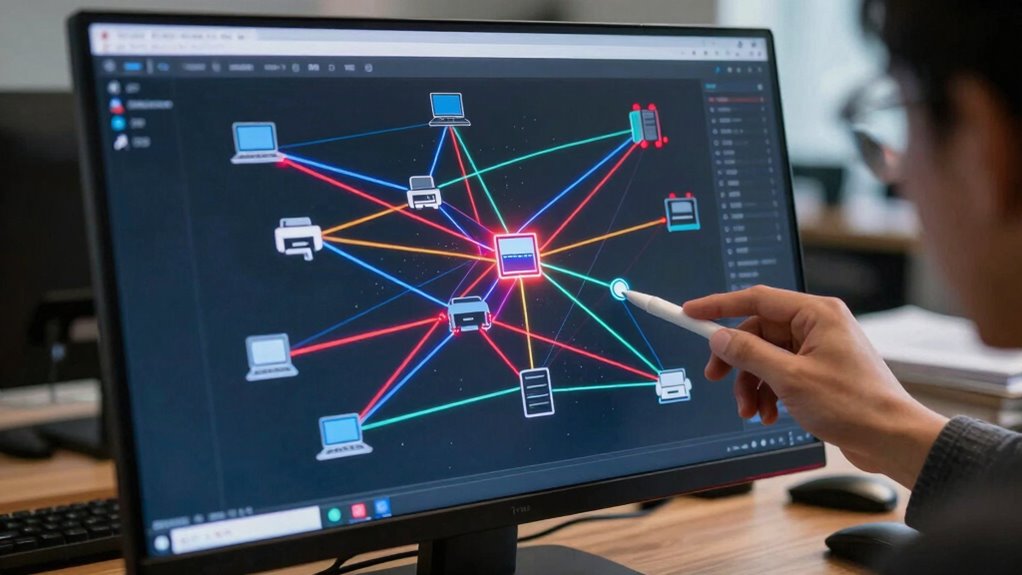
Choosing the Best Network Scanner for Your Needs

Selecting the right network scanner depends on your specific needs and the complexity of your network. If you’re focused on network security, choose a scanner that identifies vulnerabilities and unauthorized devices quickly. For device management, look for tools that provide detailed device inventories and real-time updates. Consider whether you need a lightweight scanner for small networks or a more robust solution for larger, more complex setups. Compatibility with your operating system and ease of use are also vital. Some scanners offer automation features, saving you time and reducing errors. Ultimately, the best choice aligns with your security priorities and management goals, helping you maintain a clear, up-to-date network map that reveals unknown devices and strengthens your overall network health. Incorporating top car protection and accessories can also help safeguard your network-connected vehicle systems. Ensuring your scanner has user-friendly interfaces can make ongoing management more efficient and less frustrating. Additionally, understanding early detection techniques can significantly improve your ability to identify and mitigate potential threats before they escalate. Being aware of network mapping strategies can further enhance your capacity to visualize and control all connected devices effectively.

TOPDON ONE Bidirectional Scan Tool, 10.1" OBD2 Scanner with J2534 Pass-Thru and ECU Coding, Over 50 Resets, Topology Mapping Car Diagnostic Tool for All Vehicles
Dual WiFi & 10.1" Touchscreen: Provides a stable, high-speed wireless link 3x faster than Bluetooth, and a responsive,…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Building Your First Network Map Made Simple
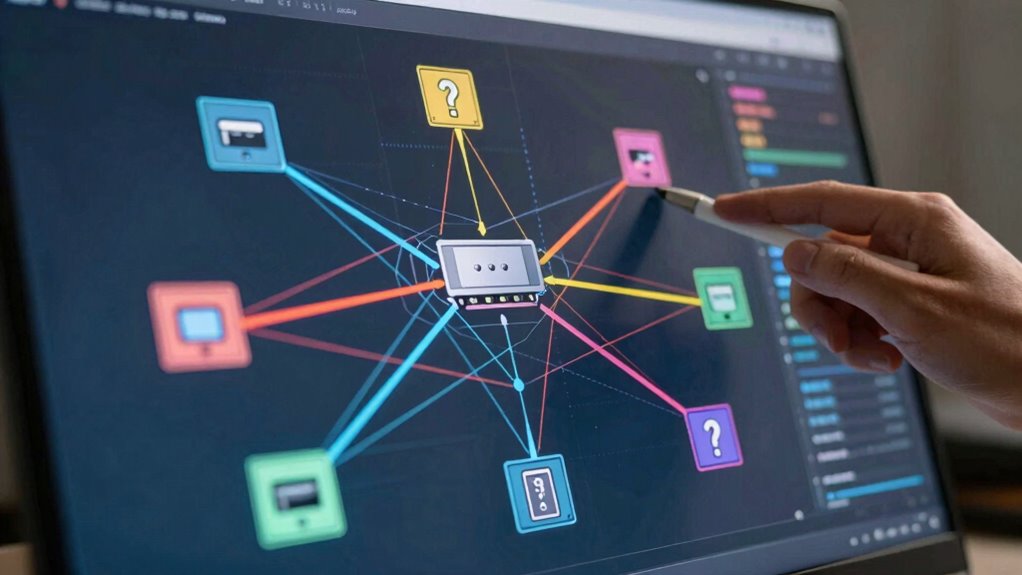
Once you’ve chosen the right network scanner, the next step is to start building your first network map. Begin by analyzing your network’s topology, which shows how devices connect and communicate. Focus on visualizing the layout, including routers, switches, and connected devices. Use the scanner’s tools to identify each device and categorize them accordingly, such as servers, printers, or workstations. This device categorization helps you understand your network’s structure and spot potential vulnerabilities. Keep the map simple at first—avoid clutter, and only include essential devices. As you gain confidence, you can add more details or expand the map. Building this initial map provides a clear view of your network, making it easier to manage and troubleshoot later.

Tera Barcode Scanner Wireless 1D Laser Cordless Barcode Reader with Battery Level Indicator, Versatile 2 in 1 2.4Ghz Wireless and USB 2.0 Wired
Larger battery enables longer continuous usage and twice the stand-by time. With the unique battery indicator light showing…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
How to Recognize and Identify Devices on Your Map

How can you accurately recognize and identify devices on your network map? Start by analyzing device fingerprints, which reveal unique characteristics like manufacturer details and device types. Use IP addressing to distinguish devices based on their assigned IP addresses, noting patterns or ranges. To improve identification, consider these tips:
Identify network devices accurately using fingerprints, IP addresses, MAC info, and behavior patterns for better security and management.
- Check device MAC addresses for manufacturer info
- Cross-reference IP addresses with your DHCP lease table
- Observe device behavior and communication patterns
- Use network scanning tools to gather detailed device info
- Look for known device signatures or fingerprints
- Incorporate device fingerprinting techniques to enhance detection accuracy. Additionally, understanding network device identification methods can further streamline this process. Exploring fandom research methods can also provide insights into behavior patterns that help distinguish device types. Employing network security principles can further improve your ability to accurately recognize devices on your map. Applying device classification methods can help you categorize and manage devices more effectively. Combining device fingerprinting with IP addressing helps you confidently recognize each device’s role and origin. This process streamlines management, enhances security, and makes your network map more accurate and useful.
Troubleshooting Common Issues When Mapping Your Network
Mapping your network can be challenging, especially when you encounter unexpected issues or discrepancies. One common problem is incomplete device detection, often caused by network security settings or device authentication barriers. Make sure your scanning tools have proper permissions and are configured to bypass firewalls or filtering rules. Sometimes, devices hide behind VLANs or use network isolation, making them hard to detect. Check your network security protocols to verify they aren’t blocking essential traffic. Also, confirm that your device discovery methods support all device types. If certain devices still don’t appear, manually verify their presence through logs or access points. Troubleshooting these issues helps you create an accurate, thorough network map, improving security and device management. Additionally, understanding network security protocols can help you identify and resolve potential barriers to device detection more effectively. Being aware of regional differences in device detection, such as those found in areas like Florida or Tennessee, can also influence your troubleshooting approach. Recognizing how regional network configurations impact device visibility can further refine your troubleshooting strategies. Moreover, considering environmental factors like water-related interference can sometimes be relevant in specialized setups or outdoor environments. Incorporating network topology concepts can also aid in visualizing and diagnosing connectivity issues more efficiently.
Frequently Asked Questions
How Often Should I Update My Network Map?
You should update your network map regularly, ideally every few months or whenever you add new devices. Keeping your network topology current guarantees your device inventory stays accurate, helping you spot unauthorized devices and troubleshoot issues quickly. Frequent updates also help you understand how your network evolves, maintaining security and performance. Don’t wait too long—stale maps can lead to overlooked vulnerabilities or overlooked device changes.
Can I Use Free Tools to Create a Network Map?
Yes, you can use free tools to create a network map that helps you understand your network topology and perform device discovery. These tools often scan your network to identify connected devices, giving you a clear visual overview. While free options may have limitations, they’re effective for small to medium-sized networks. Using them regularly helps you keep track of devices, monitor changes, and enhance your network’s security.
What Security Risks Are Associated With Network Mapping?
Network mapping is like opening a door to hidden dangers—you expose device vulnerabilities that hackers could exploit. You risk unauthorized access if your network details fall into the wrong hands. Using tools without proper security measures can create blind spots, making your network a target. Always secure your mapping process with strong passwords and encryption, so you don’t unwittingly invite cyber threats while trying to understand your network better.
How Can I Detect Hidden or Rogue Devices?
You can detect hidden or rogue devices through device identification tools that scan your network in real-time. These tools help you spot unfamiliar devices, enabling rogue device detection. Regularly reviewing your network map and comparing it with authorized device lists also reveals unauthorized connections. Keep your network secure by monitoring for unknown devices, promptly identifying potential threats, and ensuring only trusted devices are connected.
Is It Necessary to Map a Small Home Network?
Mapping a small home network isn’t always necessary, but it’s highly beneficial for device identification and network troubleshooting. Creating a simple map helps you see all connected devices, spot unauthorized ones, and understand your network’s layout. This proactive approach makes troubleshooting easier, improves security, and guarantees your devices are functioning correctly. Even in small setups, a network map offers valuable insights, keeping your home network secure and efficient.
Conclusion
By now, you see how creating a network map can reveal hidden devices and boost your security. With the right scanner and a clear plan, you can navigate your network confidently. Remember, “A stitch in time saves nine”—addressing issues early keeps your network secure. Keep mapping, stay vigilant, and you’ll always know what’s connected, making your network safer and more reliable.









